
|
Network Tunneling |
|
Usually when a client needs to connect to server it is assumed that direct connection can be established. Nowadays though, due to security reasons or network topology, it is often necessary to use a proxy or bypass a firewall. This article describes different ways to connect to PostgreSQL server with PgDAC.
Direct connection to server means that server host is accessible from client without extra routing and forwarding. This is the simplest case. The only network setting you need is the host name and port number. This is also the fastest and most reliable way of communicating with server. Use it whenever possible.
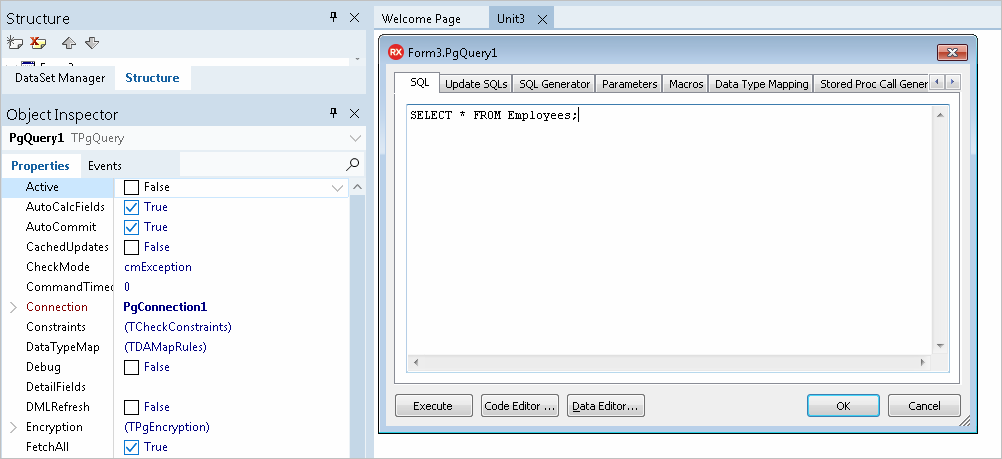
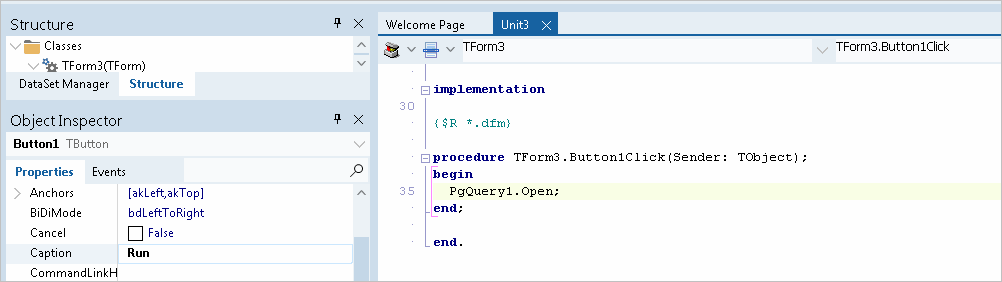
The following code illustrates the simplicity:
PgConnection := TPgConnection.Create(self);
PgConnection.Server := 'localhost';
PgConnection.Port := 5432;
PgConnection.Username := 'postgres';
PgConnection.Password := 'postgres';
PgConnection.Connect;Sometimes client machines are shielded by a firewall that does not allow you to connect to server directly at the specified port. If the firewall allows HTTP connections, you can use PgDAC together with HTTP tunneling software to connect to PostgreSQL server. PgDAC supports HTTP tunneling based on the PHP script.
An example of the web script tunneling usage can be the following: you have a remote website, and access to its database through the port of the database server is forbidden. Only access through HTTP port 80 is allowed, and you need to access the database from a remote computer, like when using usual direct connection.
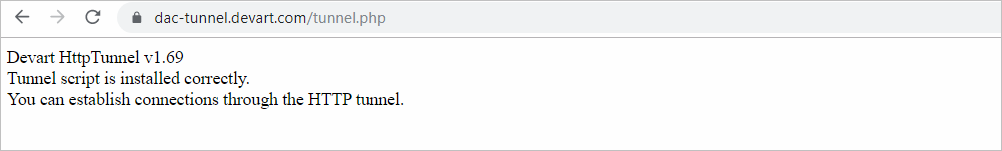
You need to deploy the tunnel.php script, which is included into the provider package, on the web server. It allows access to the database server via HTTP tunneling. The script must be accessible through the HTTP protocol. You can verify if it is accessible with a web browser. The script can be found in the HTTP subfolder of the installed provider folder, e. g. %Program Files%\Devart\PgDac for Delphi XX\HTTP\tunnel.php. The only requirement to the server is PHP 5 support.
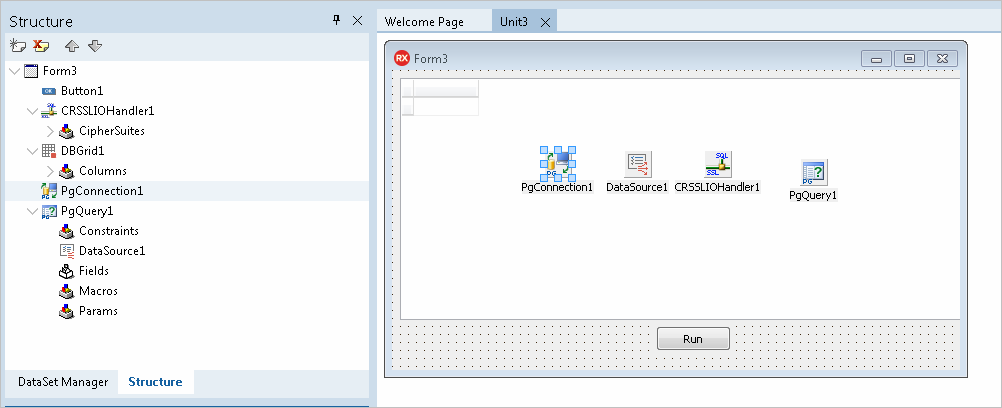
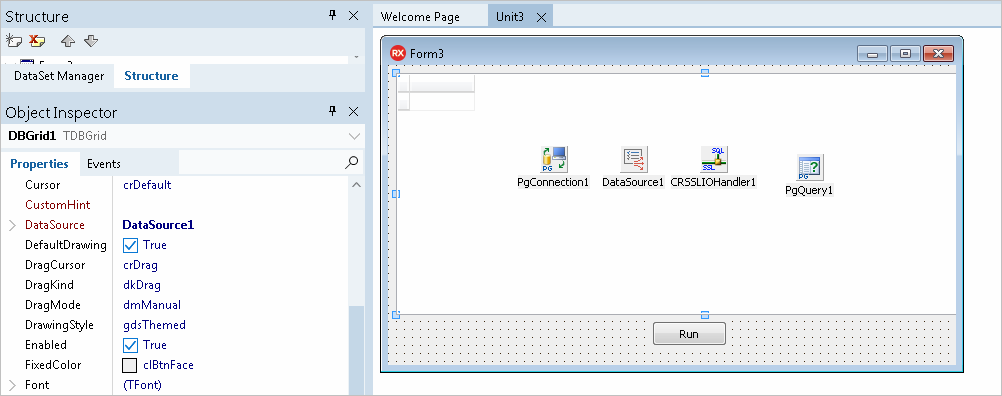
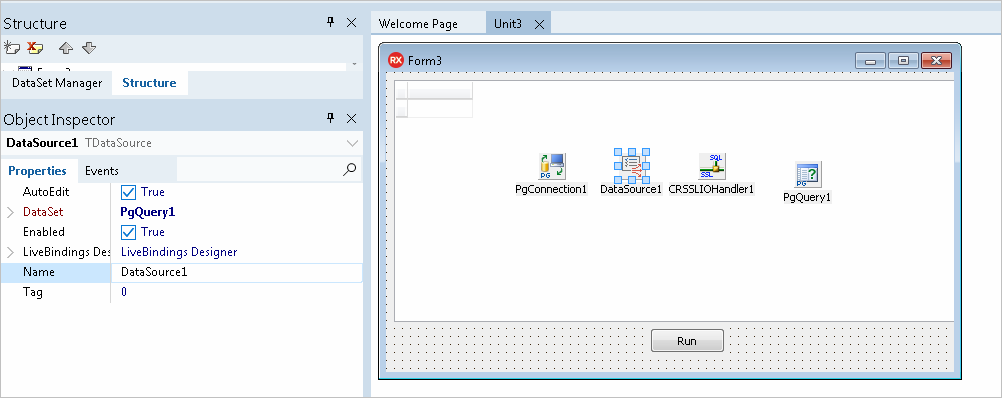
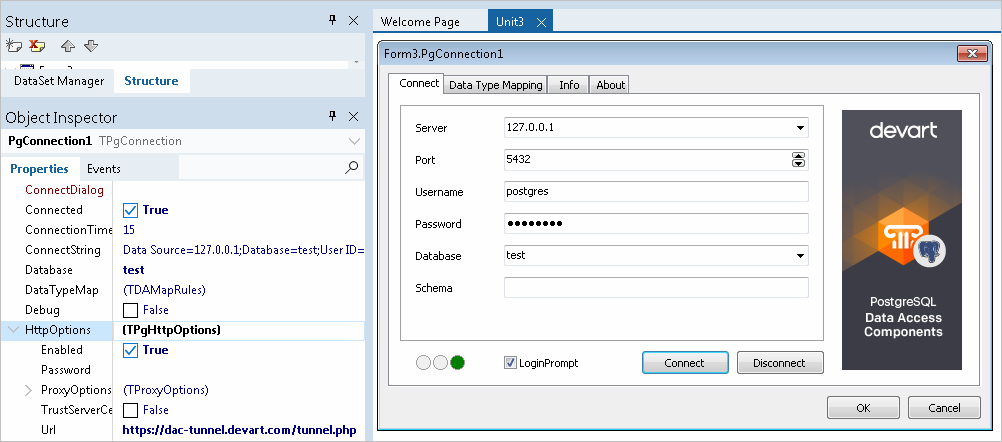
To connect to the database, you must set TPgConnection parameters for usual direct connection, which will be established from the web server side, the HttpOptions.Enabled property to True, and set the following parameters, specific for the HTTP tunneling:
| Property | Mandatory | Meaning |
|---|---|---|
| HttpOptions.Url | Yes | URL of the tunneling PHP script. For example, if the script is in the server root, the URL can be the following: http://localhost/tunnel.php. |
| HttpOptions.Username, HttpOptions.Password | No | Set these properties if the access to the website folder with the script is available only for registered users authenticated with user name and password. |
The HTTP tunneling server may be not directly accessible from the client machine. For example, client address is 10.0.0.2, server address is 192.168.0.10, and the PostgreSQL server listens on port 5433. The client and server reside in different networks, so the client can reach it only through proxy at address 10.0.0.1, which listens on port 808. In this case in addition to the TPgConnection.HttpOptions options you have to setup a HttpOptions.ProxyOptions object as follows:
PgConnection := TPgConnection.Create(self);
PgConnection.Server := '192.168.0.10';
PgConnection.Port := 5433;
PgConnection.Username := 'postgres';
PgConnection.Password := 'postgres';
PgConnection.HttpOptions.Enabled := True;
PgConnection.HttpOptions.Url := 'http://server/tunnel.php';
PgConnection.HttpOptions.ProxyOptions.Hostname := '10.0.0.1';
PgConnection.HttpOptions.ProxyOptions.Port := 808;
PgConnection.HttpOptions.ProxyOptions.Username := 'ProxyUser';
PgConnection.HttpOptions.ProxyOptions.Password := 'ProxyPassword';
PgConnection.Connect;Note that setting parameters of PgConnection.HttpOptions.ProxyOptions automatically enables the use of of the proxy server.

There is one more way to tunnel network traffic. The Secure Shell forwarding, or SSH, can be used for forwarding data. However, main purpose of SSH is traffic encryption rather than avoiding firewalls or network configuration problems. The Connecting via SSH article describes how to use SSH protocol in PgDAC.
Keep in mind that traffic tunneling or encryption always increases CPU usage and network load. It is recommended that you use direct connection whenever possible.